when preloads go sideways
How hard is it to preload a PC with the software it needs to work? Really fucking hard.
superfish
Some time ago, Lenovo shipped some computers with a surprise gift: SuperFish. I like to imagine the business development units from each company in a meeting:
Superfish: It will add value!
Lenovo: How does that work exactly?
You give us customer eyeballs. In return, we give you money. Money is value.
But how does that add value for the customer?
Well, it’s their eyeballs we’re buying. Do the math!
Sold!
aftermath
Afterwards, we’d naturally expect various other vendors to take a look at the giftware they were bundling. Hahaha. Instead of actually changing anything about their product, Dell just updated their website:
Dell is serious about your privacy
Worried about Superfish? Dell limits its pre-loaded software to a small number of high-value applications on all of our computers. Each application we pre-load undergoes security, privacy and usability testing to ensure that our customers experience the best possible computing performance, faster set-up and reduced privacy and security concerns.
I thought this was in poor taste, even at the time. There’s a certain form one should follow when shitting on the competition on your web site. You have to find something, anything, to rip out and delete to prove you’re leading the way forward. That’s how the game is supposed to be played.
Of course, in short order it was discovered that Dell was shipping their own root cert, which was supposed to be for testing only but nevertheless ended up adding value to customers, too. In imagining how this happened, I picture a scene like this:
Release manager: Fuck it, we’ll do it live!
trendmicro
I’ll just leave this here. I don’t know which systems ship with TrendMicro by default; I’m sure some do. If not, the local geek squad will likely be happy to assist.
mcafee
While reading the Ars review of Dell’s latest XPS 13 I noticed this fantastic screenshot:
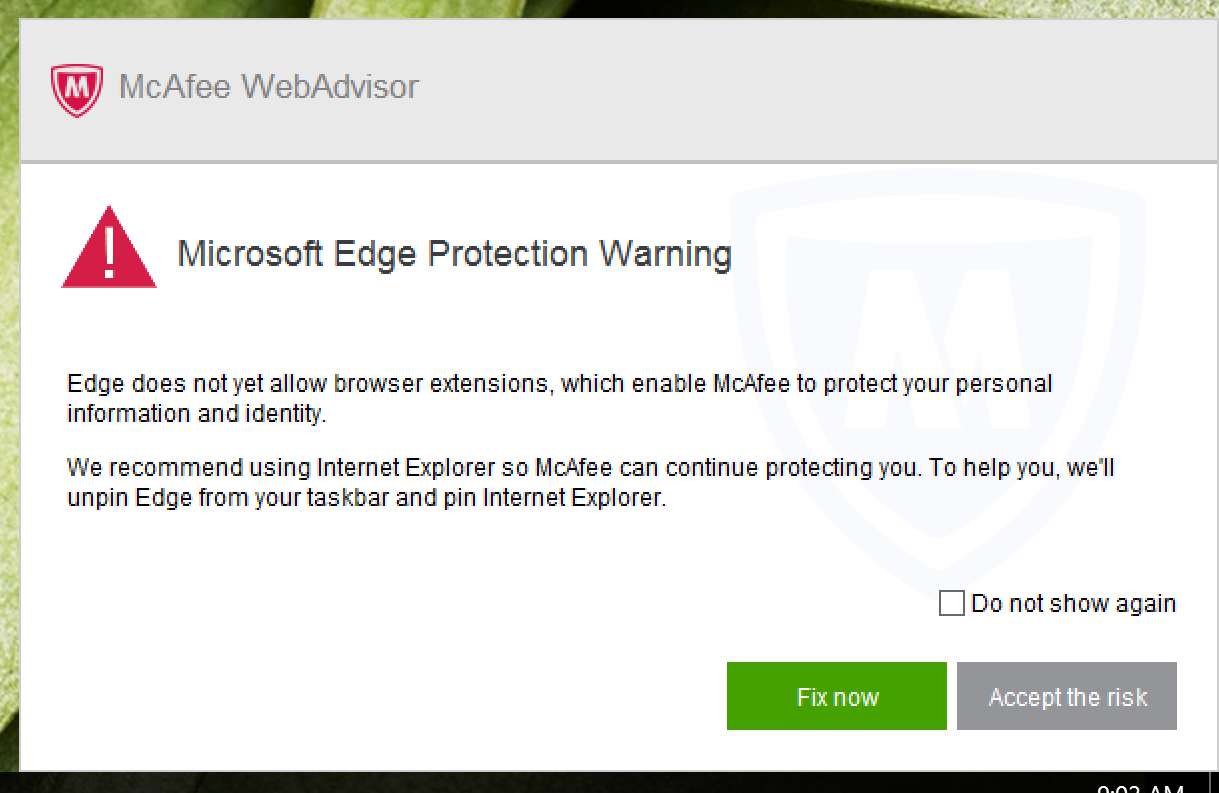
A couple observations here. This was a sample Dell sent to a professional reviewer at a fairly technical site. Did they think they wouldn’t notice this atrocity? Or they thought it was a good idea?
Think about that. Somebody at Dell took a look at that dialog box, leaned back in their Aeron, and then literally said, “This high-value application will ensure our customers have the best possible computing performance. Approved!”
I mean, what’s the alternative? Dell shipped a laptop with a software image that nobody had once even clicked on the default browser?
Second, how did this dialog come into existence? I’m normally pretty forgiving (perhaps too forgiving) of unpleasantries when it’s possibly coincidence. That’s not what happened here, though. The words “We recommend using Internet Explorer so McAfee can continue protecting you.” do not appear in a program except by deliberate action. I can just imagine:
QA files a bug report: backdoor injector fails to inject on Windows 10.
Scrumlord: Yo, developer, get that backdoor in there! You kanban do it!
Developer: But, boss, it’s really hard. There’s no extension API in Edge and I’m bad at IDA.
PM: Alright, whatever. Just switch the symlinks around. Hopefully our users are idiots anyway.
misc
Manufacturers keep doing this because people keep buying it. Are we fools or are we suckers? I’d say a bit of both. We’re fooked.
Antivirus: not the malware we need, but the malware we deserve.
I’m picking on Dell, but they’re not alone. I know my recently purchased ASUS also included McAfee. Here’s the best part. After uninstalling it, it still leaves a service not just installed, but running. Actually uninstalling McAfee in a manner that aligns with my definition of the word requires downloading a separate program (on a captcha protected web site no less, for bonus giggles) and running that. Who knows what else it does?
cert.pem
One solution would be to install an alternative operating system, like OpenBSD. Sorry, I meant to say ARCH LINUX.
I note that a fair bit of the above foolishness revolves around adding some amount of pollution to the OS’s cabal store. Maybe we can use an OS that comes with a store we trust? For example, there’s several ways a user can install OpenBSD and verify that cert.pem has only the 4943 lines it’s supposed to have. That only pushes the question back a step, however. What lines are supposed to be in this file?
“I have a diff to add a new CA to cert.pem.”
Is this CA controlled by an oppressive government?
“Yes, but Cameron promises he’s one of the good guys.”
ok tedu!
The good news is that browsers don’t actually use this file and ship their own, so when they fuck up we’re not accountable.
big brother
The trials and tribulations of bundleware mirror those of the government. For as long as most traffic was unencrypted, it was easy to inject value. But as sites started moving to full time https, the well of value started to dry up, requiring workarounds to stay in the game. Governments are facing much the same challenge, hence the large number of proposals to build a socialized, universal AV software, so that all citizens can enjoy its benefits on both desktop and mobile. How else will TrendMicro keep us safe from Let’s Encrypt?
When asked to comment, Hillary Clinton responded with a statement. “I clearly specified that the problem was to be solved by Silicon Valley’s best and brightest, not bumbling mediocrity.” Donald Trump promised to build a wall around malware and make the neckbeards pay for it. Carly Fiorina simply tweeted, “Go Iowa!”
I’m generally kind of down on TLS (and especially the CA trust model), but I guess if people are engaging in this amount of stupid to bypass it that’s a sign it could work? Still left with the unfortunate fact that TLS often remains stupid easy to bypass.