timing attacks vs interned strings
Some experiments with trying to extract strings from a Lua process via timing attacks.
more...
Some experiments with trying to extract strings from a Lua process via timing attacks.
more...
All the g2k14 summary reports from the OpenBSD Journal, plus a few relevant extras.
It’s been a week and change since the first LibreSSL portable release was announced to much sturm und drang. (To quote WP, “extremes of emotion were given free expression in reaction to the perceived constraints of rationalism”. Not be to taken too literally.) I’m not directly involved, but a few thoughts and reflections on the release and its reception. (Deliberately missing some links; do your own digging if you care.)
more...
The phrase responsible disclosure doesn’t have a precise definition. Instead, it can only be understood in terms of its opposite, irresponsible disclosure, which is defined as “any disclosure I don’t like”.
Instead of using a phrase that encodes a value judgment in place of a description, let’s pick a technical term that describes what’s happening: selective disclosure. This phrase is then neatly contrasted with its opposite, full disclosure.
Some people like the term coordinated disclosure, although in practice it often isn’t.
Also: regarding embargoes.
One of the great things about the animated GIF format, despite its many other deficiencies, is that it works everywhere. Even stodgy old browsers can display it. Naturally, this fact means that whenever an animated GIF is uploaded to twitter, they convert it to a format that fewer browsers can display.
The “Download File” text floating towards the bottom left links to an MP4 file of what was once the GIF. Just one more way developers are working to make the web a better place. Thanks guys!
After the recent OpenBSD hackathon, I took a day off to chill out in Trieste before flying home. In the mean time, a blog post regarding the perils of getpid wrapping appeared. Unfortunately, by the time I made it home and reconnected to the tubes, kettenis and bcook had already fixed the bug, before I even had a chance to shit my pants. The gall of some people.
more...
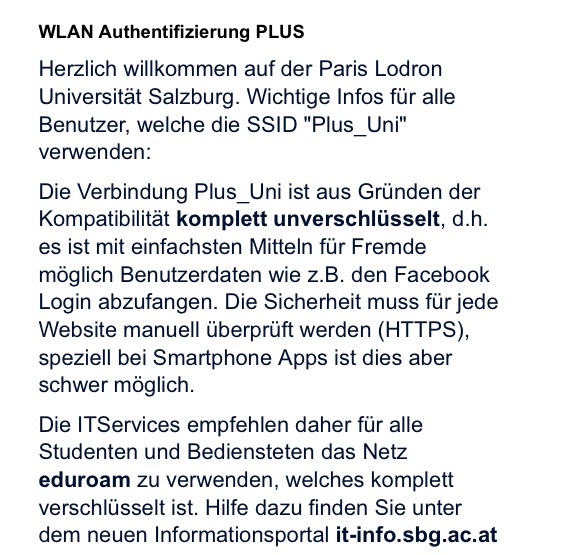
Basically: the network is insecure; the bad guys can steal your Facebook login; check that you are using HTTPS. I’ve never seen a wifi warning this clear and direct before. Bonus points for mentioning that smartphone apps are a particular weakness.
A special Fourth of July post. If you love America, you’ll love the Welcome to Night Vale podcast. It does a great job walking the line between mocking the nutjobs who believe in world government black helicopters and the sheeple who don’t. A little something for everyone to hate.
The whole show, every episode, plays with credulity, but one segment from episode 14, “The Man in the Tan Jacket”, was in a category of its own. It’s not the most absurdly comical segment, but a striking reminder of the typical internet discussion regarding the relative probability of just about anything.
Early Saturday morning, Fun Complex cameras picked up blurry motion near the soda machine. The footage is quite fuzzy and difficult to discern. Perhaps it is merely rats or racoons digging through an uncovered supply of junk food. But it is, of course, much more likely that a lost nation of people, living in the bowels of a small town blowing alley, are finally revealing themselves. Taking our food supplies and preparing for war. ... It takes very little extrapolation to believe that they worship a god named Huntocar, who demands sacrifice to keep their underground city thriving in the absence of nourishing sunlight. And a fair assumption is that they are ruled by a child king, recently coronated, who is too weak to reign back the generals intent on marching upon us in war.
From time to time, somebody posts an unsourced account of that time the Secret Service tasered their cat because they googled for “how to make money”. As it makes the rounds of all the user news sites, somebody will inevitably post a comment pointing out some logical inconsistencies in the original and asking how the more fanciful events may have transpired. Someone will then reply, explaining everything with no facts and fewer sources. And finally comes the third comment, my favorite. “I’m pretty sure that’s what happened.”
A few notes regarding agl’s post on encrypting streams and tools I’ve worked on.
signify will only verify a message if it is entirely correct. The OpenBSD installer doesn’t stream install files through tar anymore. This was something we needed to change precisely because of the situation Adam warns about. Instead the full tar file is downloaded, verified, and then extracted. Tainted data never hits the real file system.
pkg_add combined with signify works a little differently, instead checking the checksum of each file, but the tainted data is first saved to temporary files before being renamed. I’m less familiar with the exact details, but a quick chat with espie said it should be safe.
reop, which is a true encryption at rest tool, does in one sense repeat the mistakes of 20 years ago. Each message is encrypted as a single large “packet”. However, the entire message must decrypt and authenticate successfully before any output is produced, so it’s actually safer than a small packet streaming program which may produce partial output. (reop cheats a bit by imposing a message size limit; it simply can’t encrypt large files, for large values of large.)
Just watched the season 3 episode of The Good Wife, “Bitcoin for Dummies”. For an episode that aired more than two years ago, that’s pretty edgy, especially considering what I assume to be the show’s target audience. It’s fictionalized, but it does a pretty good job of depicting Bitcoin accurately. Unlike another show that simply namedropped Bitcoin to prove it was the future, the episode actually spent considerable time explaining and incorporating Bitcoin into the plot. There’s talk of the exchange rate, the crash, mining, hoarding, etc. All the more remarkable for airing in January 2012.
The plot revolves around the government’s pursuit of “Mr. Bitcoin”, played by guest star Jason Biggs, for creating an illegal currency. Naturally, this brings up the question of whether Bitcoin counts as a currency or a commodity for bartering. Linguistic analysis is used to unmask Mr. Bitcoin based on his manifesto. A hidden message is found in the blockchain. There’s also some of the usual TV IP tracking hijinks, of course, but otherwise it’s well done.
This is the only legal drama I’ve ever seen that included the phrase “preimage resistance”. Also, funny line: “Cryptographer jealousy. The ugliest kind.”
I’m pretty impressed with The Good Wife. The writers are obviously working in (then) current trends, but I think it’s fair to say they’re using them as inspiration, and not just chasing ratings with buzzwords. The portrayals seem pretty accurate and not unusually contrived. Another episode deals with a judge accepting a juror’s friend request. Real life relation. The episode where they extract information (metadata, anyone?) from redacted government files was also a winner.
The WSJ has a longer recap if you’re more interested in what Alicia and Diane were wearing than Bitcoin.